I previously wrote about Belgian banks & SSL. Updated version (15/02/2015) here.
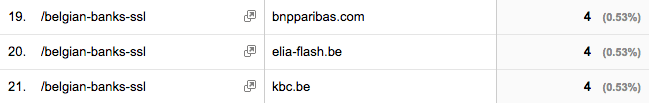
Going through my Google Analytics I noticed some noteworthy network domains, which Google discribes as “The fully qualified domain names of your visitors’ Internet service providers (ISPs)”.
There are a few more (Belgian) government institutions and universities, and the top in the list are “(not set)” and “unknown”.
Clearly some people at the banks read the post during their work time. So it’s only fair to recheck the websites… Here goes:
Those that I hadn’t tested before:
- CPH: B
- Record Bank (internet banking): F
Those that did not change:
- Rabobank: A+
- Belfius: A-
- AXA: B
- beobank: B
- KBC: B
- Keytrade Bank: B
- Crelan (internet banking): B
- Hello bank!: C
- Bank Van Breda (internet banking): C
- ING: F
- Argenta (internet banking): F
Those that did change:
- Triodos: A to A+
- downgrade prevention correctly applied.
- BNP Paribas Fortis: F to A-
- No longer vulnerable to POODLE,
- Disabled SSL3 (insecure),
- Disabled RC4 (insecure),
- Still using a weak signature (SHA1),
- No Forward Secrecy.
- bpost bank: F to A-
- No longer vulnerable to POODLE,
- Disabled SSL3 (insecure),
- Disabled RC4 (insecure),
- Still using a weak signature (SHA1),
- No Forward Secrecy.
Huge thumbs up for these last three banks! Well done, especially BNP & bpost! 🙂
Keep on shaming the others.
The entire list updated:
Grade A
- Rabobank (A+): no known issues. Support for HTTP Strict Transport Security and prevented downgrade attacks.
- Triodos (A+): no known issues. Support for HTTP Strict Transport Security and prevented downgrade attacks.
- Belfius (A-): weak signature (SHA1), no Forward Secrecy.
- BNP Paribas Fortis: (A-) weak signature (SHA1), no Forward Secrecy.
- bpost bank: (A-) weak signature (SHA1), no Forward Secrecy.
Grade B
- AXA: weak signature (SHA1), SSL3 (insecure), RC4 (insecure), no Forward Secrecy.
- beobank: weak signature (SHA1), no TLS 1.2, RC4 (insecure), no Forward Secrecy.
- CPH: no TLS 1.2, RC4 (insecure), no Forward Secrecy.
- KBC: weak signature (SHA1), no TLS 1.2, no Forward Secrecy.
- Keytrade Bank: weak signature (SHA1), RC4 (insecure).
- Crelan: no SSL on main page.
- internet banking: weak signature (SHA1), SSL3 (insecure), no TLS 1.2, RC4, no Forward Secrecy.
Grade C
- Hello bank!: vulnerable to POODLE attack, weak signature (SHA1), RC4 (insecure).
- Bank Van Breda: no SSL on main page.
- internet banking: vulnerable to POODLE attack, weak signature (SHA1), no TLS 1.2, no Forward Secrecy.
Grade D
- n/a
Grade E
- n/a
Grade F
- ING: vulnerable to POODLE attack, SSL3 (insecure), weak signature (SHA1), RC4 (insecure), no Forward Secrecy.
- Argenta: no SSL on main page.
- internet banking: vulnerable to POODLE attack, SSL3 (insecure), weak signature (SHA1), RC4 (insecure), no Forward Secrecy.
- Record Bank: no SSL on main page.
- internet banking: vulnerable to POODLE attack, RC4 (insecure), no Forward Secrecy.
Information about SSL Labs grading can be found here. Grade A (+) being the best possible ranking, and F the worst.
Leave a Reply…