Category: Networking
-
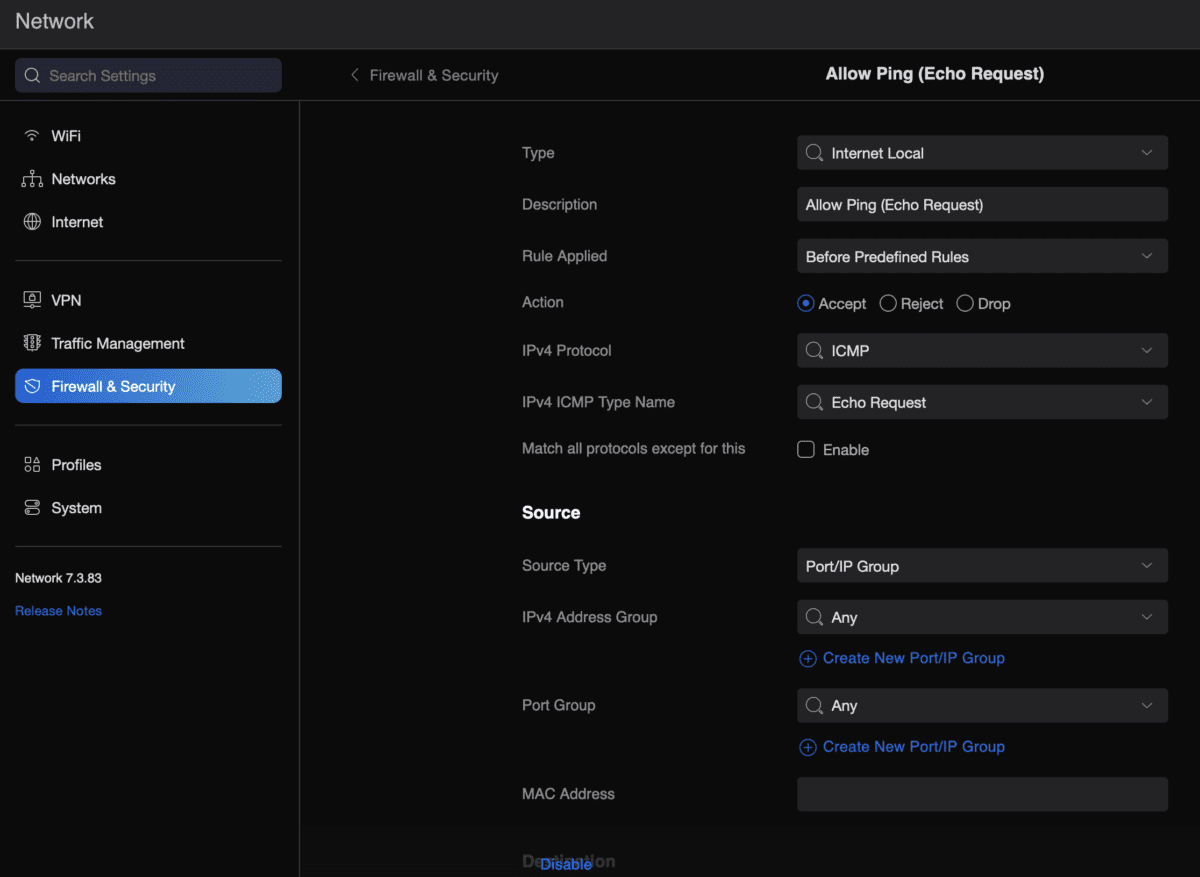
Allow ping from USG
Because I keep forgetting and it takes me far too much time to go through one of my million sites where I set this up and find the right config… To allow a USG (Unifi Security Gateway) to reply to external (WAN) ping requests, do the following: That’s it… All this for Smokeping.
-

Ikea Tradfri with Philips Hue
Recently visited Ikea and had to get a Christmas star-light like I used to have during my childhood. Most of my (non-track) light at home is smart using either a TP-Link Kasa smartplug or Philips Hue (and I want to avoid adding more brands, more apps, and more shit). However, Philips Hue is quite $$$…
-

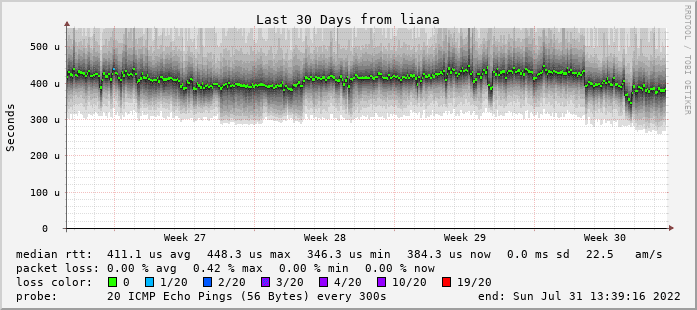
Smokeping.eu
I’ve revamped my Smokeping infra a bit since 2020. First off, starting to use the smokeping.eu1 domain that Bianco got 10 or so years ago instead of using weird URLs under superuser.one domain. It’s running on four nodes as we speak: a virtual machine on a colocation server in Leaseweb, Amsterdam, NL -> leaseweb.nl.smokeping.eu a…
-

Remote desktop and Wake-on-LAN
Shan uses her iPad a lot, but a lot of the more serious (interior design) work needs to happen on AutoCAD or Photoshop. That is just not going to work on an iPad. When we’re travelling (read: holiday) she’s carrying an old Lenovo ThinkPad 13 (great device!) just “in case” she needs to open AutoCAD…
-
Encryption
-
Sony stops DNS resolvers
The Hamburg Regional Court today ruled that they would not suspend an existing injunction against Quad9 in a case filed by Sony Music Germany. The case centers around Sony Music’s demand that Quad9’s servers located in Germany stop resolving DNS names of third-party sites which are claimed to have URLs that contain copyright infringements. Source.…
-

Xiaomi Phone Shipped With Censorship List
This summer, the Lithuanian government went public with an astounding finding. A Xiaomi phone sold in Europe — the Mi 10T 5G — could censor approximately 450 words and phrases, it said. The blocklist wasn’t active, but could be activated remotely. It was filled with political terms, including “Democratic Movement” and “Long live Taiwan’s independence.”…
-

Ideal travel router: GL-AR750S
Right. With the pandemic and all none of us are going to travel much but still… About a year ago I purchased myself an OpenWRT router to use on the plane and in hotels. And so far I really like both the device and the Hong Kong based brand (launching new and updated products, and…
-

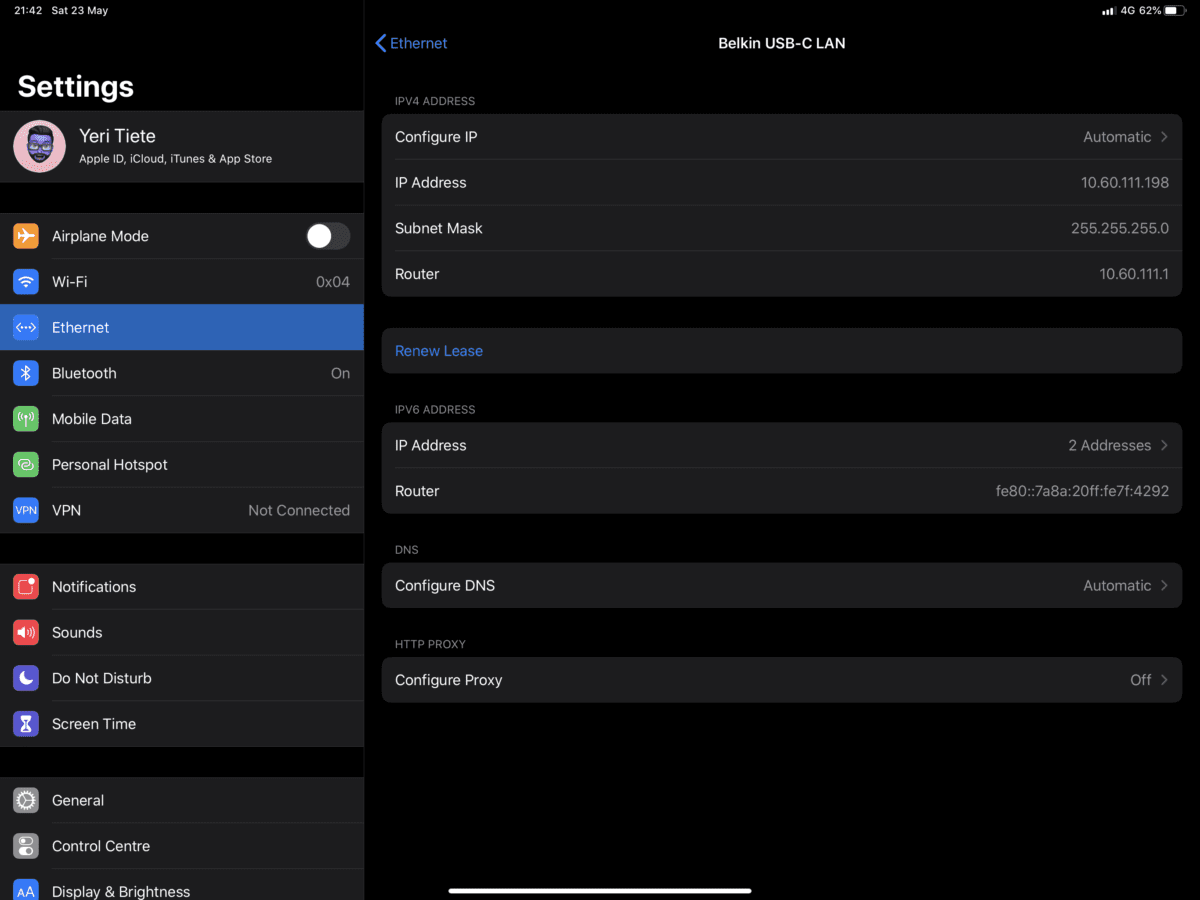
iPad Pro USB-C Ethernet
I’ve had an iPad Pro with the new Magic Keyboard and one of the things I’ve been wondering… Say I am stuck in a datacenter and I need to ssh through wired networking to a server — sure I’ll definitely rather use my Mac laptop, but just in case… But would it actually work? The…