Category: Windows
-

Remote desktop and Wake-on-LAN
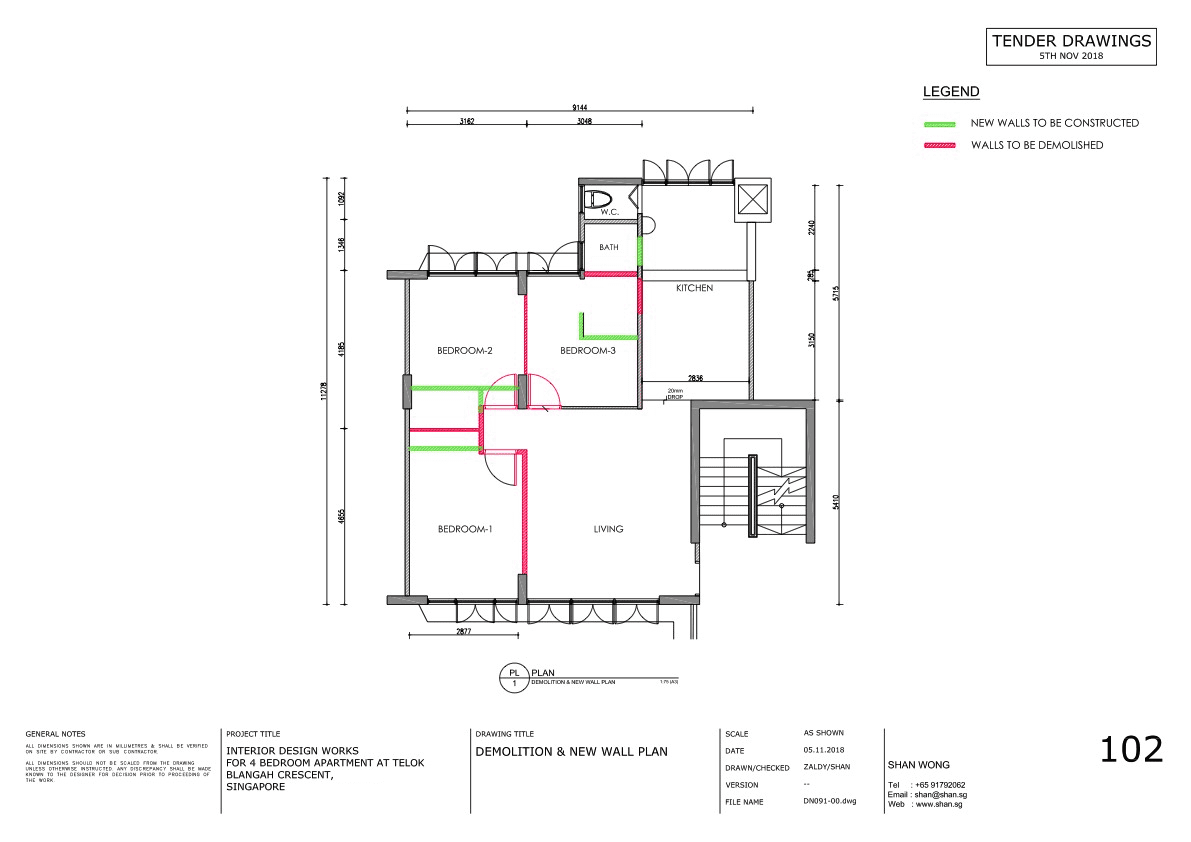
Shan uses her iPad a lot, but a lot of the more serious (interior design) work needs to happen on AutoCAD or Photoshop. That is just not going to work on an iPad. When we’re travelling (read: holiday) she’s carrying an old Lenovo ThinkPad 13 (great device!) just “in case” she needs to open AutoCAD…
-

Screen going black with AutoCAD (LT)
I am not sure what is the problem — I’ve upgraded Shan’s 27″ 2k monitor to a 32″ 4k monitor and AutoCAD LT recently updated from 2021 to 2022. Shan‘s been using a 2017 i5 NUC (NUC7i5BNB) with 32Gb RAM using the onboard GPU. Something that should be plenty for a bit of Windows, Chrome,…
-
Belgian banks & SSL — part 3
EDIT: ING is now A- (not reflected in this blog post). EDIT 2: Keytrade & Hello Bank also went to A. I’ll post a new blog post later tonight. EDIT 3: Updated post here. Part three, or how I single-handedly “fixed” SSL at the Belgian banks. 😉 Part one and two are available here. Not related…
-
Belgian banks & SSL — part 2
I previously wrote about Belgian banks & SSL. Updated version (15/02/2015) here. Going through my Google Analytics I noticed some noteworthy network domains, which Google discribes as “The fully qualified domain names of your visitors’ Internet service providers (ISPs)”. There are a few more (Belgian) government institutions and universities, and the top in the list are “(not…
-
Belgian banks & SSL
Tested using SSL Labs on 20/01/2015. Updated version 01/02/2015 here and 15/02/2015 here. Only providing the weak points. Once there is one SHA1 key in the chain, I will report everything as weak. Check SSL Labs for a full report, including what they actually did good (if anything). Grade A Rabobank (A+): no known issues. Support for HTTP…
-
5 Reasons The Guy Fixing Your Computer Hates You
-
Office 2010: cannot verify the license for this product
Due to continuous Access errors, I decided to reinstall Office Professional 2010 (64 bit). As I couldn’t find the original CD key I installed it with, I used another one from another installation. So far so good, installation went fine, etc. Once I started any Office app, it popped up this error: “Microsoft Office professional plus 2010…
-
Windows 8
I lolled.
-
*oops*