Unifi u6+ failing to upgrade
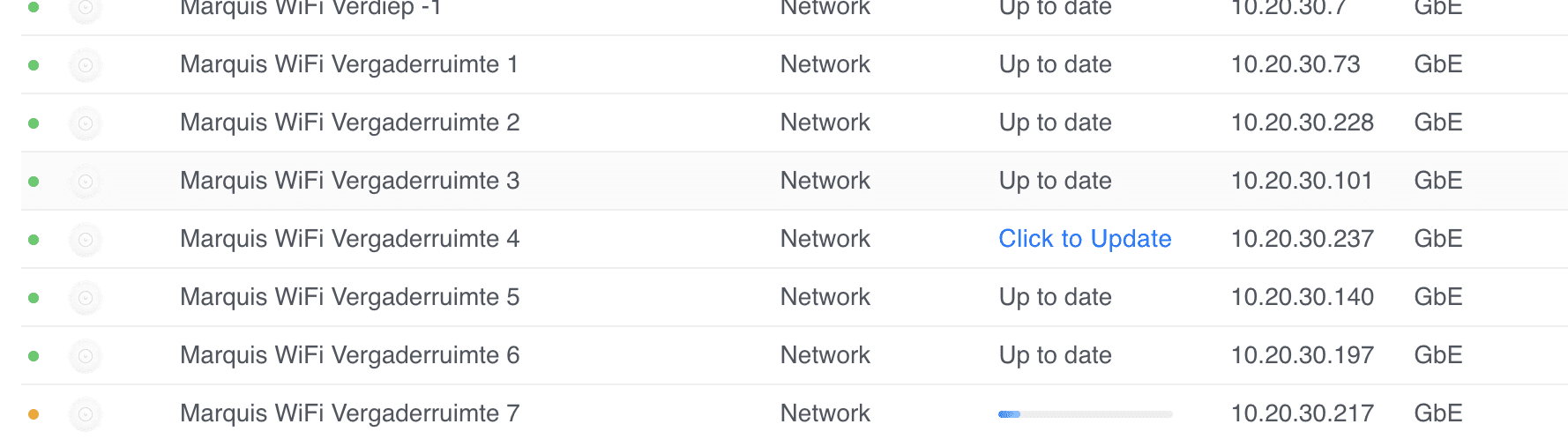
I have quite a few sites where some Unifi U6+ Access Points fail to upgrade with a generic update failed message.
Marquis WiFi Vergaderruimte 4 update failed.
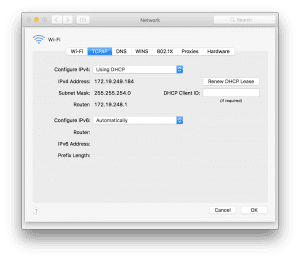
I've tried everything, from ssh'ing, factory resetting with set-default, to manually upgrading with upgrade, etc.
Nothing worked. I thought I had a bunch of bad APs (and many had their warranty expire by a few weeks or months).
As a last resort, I decide to reach out to Ubiquiti's support. First line wasn't very helpful, but as the case was escalated, I've managed to recover and properly update the APs.